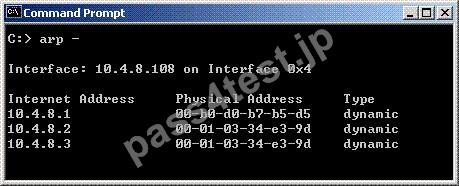
In a Load Sharing Unicast mode scenario, the internal-cluster IP address is 10.4.8.3. The internal interfaces on two members are 10.4.8.1 and 10.4.8.2. Internal host 10.4.8.108 Pings 10.4.8.3, and receives replies. The following is the ARP table from the internal Windows host 10.4.8.108: c:> arp According to the output, which member is the Pivot?
A. 10.4.8.108
B. 10.4.8.1
C. 10.4.8.3
D. 10.4.8.2
正解:D
質問 2:
You must set up SIP with a proxy for your network. IP phones are in the 172.16.100.0 network. The Registrar and proxy are installed on host 172.16.100.100. To allow handover enforcement for outbound calls from SIP-net to network Net_B on the Internet, you have defined the following objects:
Network object: SIP-net: 172.16.100.0/24
SIP-gateway: 172.16.100.100
VoIP Domain object: VoIP_domain_A
1.End-point domain: SIP-net
2.VoIP gateway installed at: SIP-gateway host object
How would you configure the rule?
A. SIP-Gateway/Net_B/sip_any/accept
B. VoIP_domain_A/Net_B/sip_any/accept
C. VoIP_domain_A/Net_B/sip_any, and sip/accept
D. SIP-Gateway/Net_B/sip/accept
E. VoIP_Gateway_A/Net_B/sip/accept
正解:B
質問 3:
Damon enables an SMTP resource for content protection. He notices that mail seems to slow down on occasion, sometimes being delivered late. Which of the following might improve throughput performance?
A. Configuring the Content Vector Protocol (CVP) resource to forward the mail to the internal SMTP server, without waiting for a response from the Security Gateway
B. Configuring the CVP resource to return the mail to the Gateway
C. Increasing the Maximum number of mail messages in the Gateway's spool directory
D. Configuring the SMTP resource to bypass the CVP resource
E. Configuring the SMTP resource to only allow mail with Damon's company's domain name in the header
正解:A
質問 4:
You receive an alert indicating a suspicious FTP connection is trying to connect to one of your internal hosts. How do you block the connection in real time and verify the connection is successfully blocked?
A. Highlight the suspicious connection in SmartView Tracker > Log mode. Block the connection using Tools > Block Intruder menu. Use the Log mode to confirm that the suspicious connection is dropped.
B. Highlight the suspicious connection in SmartView Tracker > Log mode. Block the connection using Tools > Block Intruder menu. Use Log mode to confirm that the suspicious connection does not reappear.
C. Highlight the suspicious connection in SmartView Tracker > Active mode. Block the connection using Tools > Block Intruder menu. Use Active mode to confirm that the suspicious connection is dropped.
D. Highlight the suspicious connection in SmartView Tracker > Active mode. Block the connection using the Tools > Block Intruder menu. Use the Active mode to confirm that the suspicious connection does not reappear.
正解:D
質問 5:
You configure a Check Point QoS Rule Base with two rules: an H.323 rule with a weight of
10, and the Default Rule with a weight of 10. The H.323 rule includes a per-connection guarantee of 384 Kbps, and a per-connection limit of 512 Kbps. The per-connection guarantee is for four connections, and no additional connections are allowed in the Action properties. If traffic passing through the QoS Module matches both rules, which of the following statements is true?
A. The H.323 rule will consume no more than 2048 Kbps of available bandwidth.
B. Neither rule will be allocated more than 10% of available bandwidth.
C. Each H.323 connection will receive at least 512 Kbps of bandwidth.
D. 50% of available bandwidth will be allocated to the Default Rule.
E. 50% of available bandwidth will be allocated to the H.323 rule.
正解:A
質問 6:
Which Security Servers can perform Content Security tasks, but CANNOT perform authentication tasks?
A. Telnet
B. SMTP
C. HTTP
D. FTP
正解:B


 565 お客様のコメント
565 お客様のコメント





Koike -
試験に受かりました。覚えてきた問題が試験にも同じのが出てて良かったです。合格しました。とても感謝しています