Which object in the Symantec Endpoint Protection Manager console describes the most granular level to which a policy can be assigned?
A. User
B. Client
C. Group
D. Computer
正解:C
質問 2:
An administrator configures the scan duration for a scheduled scan. The scan fails to complete in the specified time period.
When will the next scheduled scan occur on the computer?
A. within the next hour
B. when the computer reboots
C. when the user restarts the scan
D. at the next scheduled scan period
正解:D
質問 3:
Which tool should the administrator run before starting the Symantec Endpoint Protection Manager upgrade as a Symantec Best Practice?
A. collectLog.cmd
B. LogExport.cmd
C. Upgrade.exe
D. DBValidator.bat
正解:D
質問 4:
An exception needs to be created for a file named "RunMe.exe" in a user's Windows 7 "My Documents" folder. The user's login name is Bob.
Which method should be used?
A. create a file exception for "*\RunMe.exe"
B. create a file exception for "[Drive]:\Users\Bob\My Documents\RunMe.exe"
C. create a file exception for "RunMe.exe" with a Prefix Variable of [USERNAME]
D. create a file exception for "RunMe.exe" with a Prefix Variable of %USERPROFILE%
正解:B
質問 5:
Which two Symantec Endpoint Protection components are used to distribute content updates? (Select two.)
A. Symantec Endpoint Protection Manager
B. Symantec Insight Database
C. Shared Insight Cache Server
D. Symantec Protection Center
E. Group Update Provider (GUP)
正解:A,E
質問 6:
When can an administrator add a new replication partner?
A. immediately following the first LiveUpdate session of the new site
B. immediately following a successful Active Directory sync
C. during the initial install of the new site
D. during a Symantec Endpoint Protection Manager upgrade
正解:C
質問 7:
Refer to the exhibit.
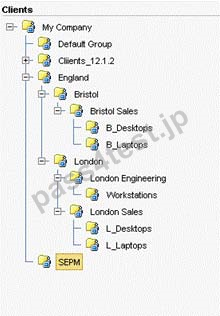
A manufacturing company runs three shifts at their Bristol Sales office. These employees currently share desktops in the B_Desktops group. The administrators need to apply different policies/configurations for each shift.
Which step should the administrator take in order to implement shift policies after switching the clients to user mode?
A. turn on Active Directory integration
B. modify the B_Desktops policy
C. create three shift policies for the Bristol group
D. create a group for each shift of users in the Bristol group
E. turn on inheritance for all groups in England
正解:D
質問 8:
Which technology can prevent an unknown executable from being downloaded through a browser session?
A. SONAR
B. Application Control
C. Browser Intrusion Prevention
D. Download Insight
正解:D


 717 お客様のコメント
717 お客様のコメント





仲*爱 -
短い時間で250-315試験に合格するには、250-315問題集を買わなければならないです。250-315問題集は素晴らしい商品です!