You are administering Veritas Volume Manager on the UNIX platform, and you need to remove the volume using vxassist command. Given the following steps:
1.Remove the volume entry from the /etc/vfstab file.
2.Remove all references to the volume by application programs.
3.Stop all Activity by VxVM on the volume using vxvol stop command.
4.Unmount the volume, which is mounted as a file system.
What are the necessary sequential steps you need to follow before removing the volume?
A. 3,1,4,2
B. 1,4,3,2
C. 2,4,3,1
D. 4,2,1,3
正解:A
質問 2:
You are consulted by a development environment administrator about a test server with Storage Foundation installed. The development administrator is facing difficulty in making changes to a complex configuration. You are required to identify the problem with the process of changing the existing configuration. What would you do to perform this task?
A. Issue the command "vxse_dg1 run" and save the output of the rule as a text file, documenting rule violations as actionable issues.
B. Issue the command "vxse_drl1 run" and save the output of the rule as a text file, documenting rule violations as actionable issues.
C. Use vxprint to visually inspect the configuration of the disk group's objects.
D. Issue the command "vxse_disklog run" and save the output of the rule as a text file, documenting rule violations as actionable issues.
正解:A
質問 3:
You have installed all the features for Storage Foundation for DB2. On the VxFS file system, you execute a command /opt/VRTS/bin/qiomkfile -s 500m /db01/dbfile.
What will be the outcome of this command?
A. The command will resize a Quick I/O file to 500 MB.
B. The command will create a concurrent I/O capable file.
C. The command will terminate without providing any result.
D. The command will create a 500 MB Quick I/O capable file.
正解:D
質問 4:
Which two actions should an organization take when deploying Endpoint Prevent according to Symantec best practices? (Select two.)
A. configure, test, and tune filters
B. enable monitoring of the local file system
C. delete the pre-defined filters and create its own
D. enable monitoring of many destinations and protocols simultaneously
E. test the agent on a variety of end-user images
正解:A,E
質問 5:
Refer to the exhibit.
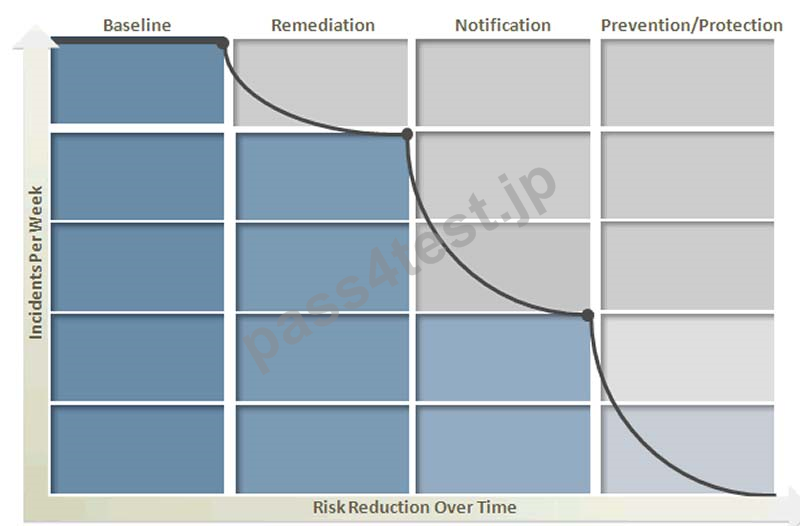
Symantec Data Loss Prevention's four phases of risk reduction model provides a blueprint for identifying and remediating key risk areas without disrupting legitimate business activity.
According to best practices, which option should be enabled during the baseline phase of policy risk reduction?
A. change automated email responses
B. enable auto-encryption
C. EDM/IDM detection
D. use secure storage
正解:C
質問 6:
A user is unable to log in as sysadmin. The Data Loss Prevention system is configured to use Active Directory authentication. The user is a member of two roles: sysadmin and remediator.
How should the user log in to the user interface in the sysadmin role?
A. domain\username
B. sysadmin\username@domain
C. username\sysadmin
D. sysadmin\username
正解:D
質問 7:
A DLP administrator needs to forward data loss incidents to the company's Security Information and Event Management (SIEM) system. Which response rule action provides the administrator with the ability to accomplish this task?
A. All: Log to a Syslog Server
B. All: Send Email Notification
C. All: Add Note
D. All: Set Attribute
正解:A
質問 8:
Which command will you run to get the full path name of the file, if you only have the inode number?
A. vxlsino
B. vxquota
C. vxfsstat
D. vxquot
正解:A


 768 お客様のコメント
768 お客様のコメント





波希** -
250-513問題集は本当にいい資料です。あなたは是非ご利用頂きます。