Which version of SNMP traps can the Cascade Profiler and Cascade Express send?
A. SNMPv2 Only
B. SNMPv1 and SNMPv2
C. SNMPv1 and SNMPv3
D. SNMPv1 Only
正解:C
質問 2:
When working with capture job traces on a Cascade Shark appliance from Cascade Pilot:
A. The capture job trace should first be indexed by right-clicking on it and selecting "Index".
B. Views should always be applied directly to the job trace.
C. Packets should be exported from the capture job trace before beginning analysis.
D. Trace clips should first be created, and views applied to them.
正解:D
質問 3:
In the Cascade Profiler Dashboard GUI, what types of content blocks can you create? (Select 4)
A. Top usernames
B. Unacknowledged Events
C. Last Day Events
D. Top items (where items are hosts, interface, etc.)
E. Current Events
F. Watched items (where items are hosts, interface, etc.)
正解:B,D,E,F
質問 4:
Some common protocols which may be observed on a network with visibility tools are listed below. Match the protocol name with the most common port used.
1.HTTP a) TCP/25
2.HTTPS b) TCP/445
3.HTTPS through a proxy c) TCP/443
4.SMTP d) TCP/80
5.CIFS e) TCP/8080
A. 1-d; 2-c; 3-e; 4-a; 5-b
B. 1-d; 2-b; 3-c; 4-a; 5-b
C. 1-e; 2-d; 3-c ; 4-b; 5-a
D. 1-e; 2-c; 3-d; 4-a; 5-b
E. 1-d; 2-c; 3-e; 4-b; 5-a
正解:A
質問 5:
Refer to the Exhibit.
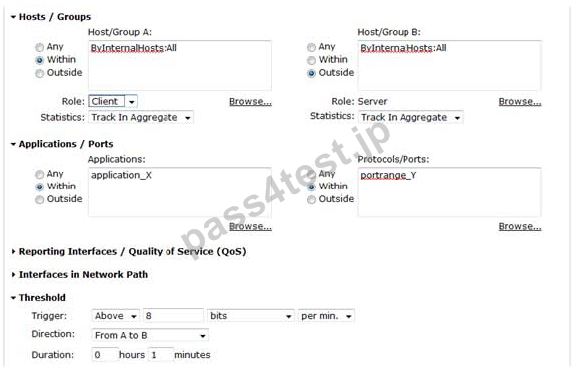
For a user defined host policy on Cascade Profiler, what would trigger this policy to generate an alert?
A. Any internal-only traffic using application "X" and port range "Y"
B. Any traffic using application "X" or port range "Y"
C. Any traffic from internal clients to external servers using application "X" or port range "Y"
D. Any traffic from internal clients to external servers using application "X" and port range "Y"
E. Any traffic between internal and external hosts using application "X" or port range "Y"
F. Any traffic between internal and external hosts using application "X" and port range "Y"
G. Any internal-only traffic using application "X" or port range "Y"
正解:D
質問 6:
Cascade Profiler is able to report traffic using two different approaches (centricities). Two approaches can result in different results when using the same report criteria due to the way data is aggregated and counted. What are these two approaches? (Select 2)
A. The Cascade Profiler does not have two approaches
B. Interface centric
C. Host centric
D. Application centric
E. Port centric
正解:B,C
質問 7:
If there is a Layer 7 fingerprint and a Layer 4 mapping for a particular application, which of the following is truE. (Select 5)
A. Care must be taken when defining reports and policies to reflect overlapping definitions and the Layer 4 override policy
B. If the Layer 4 mapping override policy is not "Unknown/Unclassified", the Layer 4 mapping applies to flows not passing a Sensor or other application fingerprinting device as well as to flows not matching any defined Layer 7 fingerprint
C. If the Layer 4 mapping override policy is "Unclassified", the Layer 4 mapping only applies to flows not passing a Sensor or other application fingerprinting device
D. If the Layer 4 mapping override policy is "Always", then the Layer 7 fingerprint will never be used for flows matching both criteria
E. The traffic Expression "app L7_fingerprint or app L4_mapping" will catch all traffic flows for the application data in a report
F. If the Layer 4 mapping override policy is "Unknown/Unclassified", the Layer 4 mapping applies to flows not passing a Sensor or other application fingerprinting device as well as to flows not matching any defined Layer 7 fingerprint
正解:A,C,D,E,F


 616 お客様のコメント
616 お客様のコメント





松木** -
一回で合格しました。この本で理解していれば、迷わず回答できる問題が9割でした。この299-01一つで充分だと思います。