Because UDP is a connectionless protocol: (Select 2)
A. There is no guarantee that the UDP packets will arrive at their destination
B. It can only be used for SYN scans
C. ICMP port unreachable messages may not be returned successfully
D. It can only be used for Connect scans
E. UDP recvfrom() and write() scanning will yield reliable results
正解:A,C
解説: (Pass4Test メンバーにのみ表示されます)
質問 2:
How do you defend against Privilege Escalation?
A. Run users and applications on the least privileges
B. Run services as unprivileged accounts
C. Use encryption to protect sensitive data
D. Allow security settings of IE to zero or Low
E. Restrict the interactive logon privileges
正解:A,B,C,E
質問 3:
Dan is conducting penetration testing and has found a vulnerability in a Web Application which gave him the sessionID token via a cross site scripting vulnerability. Dan wants to
replay this token. However, the session ID manager (on the server) checks the originating IP address as well. Dan decides to spoof his IP address in order to replay the sessionID. Why do you think Dan might not be able to get an interactive session?
A. Dan can establish an interactive session only if he uses a NAT
B. The scenario is incorrect as Dan can spoof his IP and get responses
C. Dan cannot spoof his IP address over TCP network
D. The server will send replies back to the spoofed IP address
正解:D
質問 4:
What type of port scan is shown below?
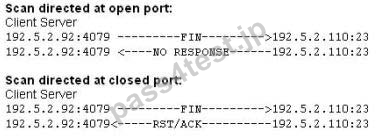
A. Windows Scan
B. FIN Scan
C. Idle Scan
D. XMAS Scan
正解:B
質問 5:
Buffer X in an Accounting application module for Brownies Inc. can contain 200 characters. The programmer makes an assumption that 200 characters are more than enough. Because there were no proper boundary checks being conducted, Bob decided to insert 400 characters into the 200-character buffer. (Overflows the buffer). Below is the code snippet:

How can you protect/fix the problem of your application as shown above?
A. Add a separate statement to signify that if we have written 200 characters to the buffer,the stack should stop because it cannot hold any more data
B. Because the counter starts with 0,we would stop when the counter is more than 200
C. Because the counter starts with 0,we would stop when the counter is less than 200
D. Add a separate statement to signify that if we have written less than 200 characters to the buffer,the stack should stop because it cannot hold any more data
正解:A,C
質問 6:
_________ is a tool that can hide processes from the process list, can hide files, registry entries, and intercept keystrokes.
A. RootKit
B. DoS tool
C. Trojan
D. Backdoor
E. Scanner
正解:A
解説: (Pass4Test メンバーにのみ表示されます)
質問 7:
When working with Windows systems, what is the RID of the true administrator account?
A. 500
B. 1024
C. 1000
D. 1001
E. 501
F. 512
正解:A
解説: (Pass4Test メンバーにのみ表示されます)
質問 8:
When discussing passwords, what is considered a brute force attack?
A. You load a dictionary of words into your cracking program
B. You attempt every single possibility until you exhaust all possible combinations or discover the password
C. You wait until the password expires
D. You create hashes of a large number of words and compare it with the encrypted passwords
E. You threaten to use the rubber hose on someone unless they reveal their password
正解:B
解説: (Pass4Test メンバーにのみ表示されます)


 868 お客様のコメント
868 お客様のコメント





佐藤** -
私は1週間前に312-50v8問題集のみを準備しましたが、高得点で試験に合格しました。