Internet Control Message Protocol (ICMP) messages occur in many situations, such as whenever a datagram cannot reach the destination or the gateway does not have the buffering capacity to forward a datagram. Each ICMP message contains three fields: type, code, and checksum. Different types of Internet Control Message Protocols (ICMPs) are identified by a type and code field.

Which of the following ICMP messages will be generated if the destination port is not reachable?
A. ICMP Type 5 code 3
B. ICMP Type 11 code 1
C. ICMP Type 3 code 3
D. ICMP Type 3 code 2
正解:C
質問 2:
You have compromised a lower-level administrator account on an Active Directory network of a small company in Dallas, Texas. You discover Domain Controllers through enumeration. You connect to one of the Domain Controllers on port 389 using Idp.exe. What are you trying to accomplish here?
A. Enumerate MX and A records from DNS
B. Enumerate domain user accounts and built-in groups
C. Establish a remote connection to the Domain Controller
D. Poison the DNS records with false records
正解:B
質問 3:
SQL injection attack consists of insertion or "injection" of either a partial or complete SQL query via the data input or transmitted from the client (browser) to the web application.
A successful SQL injection attack can:
i)Read sensitive data from the database
iii)Modify database data (insert/update/delete)
iii)Execute administration operations on the database (such as shutdown the DBMS) iV)Recover the content of a given file existing on the DBMS file system or write files into the file system v)Issue commands to the operating system
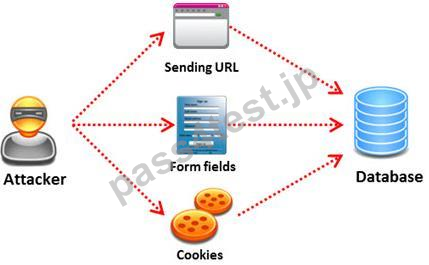
Pen tester needs to perform various tests to detect SQL injection vulnerability. He has to make a list of all input fields whose values could be used in crafting a SQL query, including the hidden fields of POST requests and then test them separately, trying to interfere with the query and to generate an error.
In which of the following tests is the source code of the application tested in a non-runtime environment to detect the SQL injection vulnerabilities?
A. Automated Testing
B. Dynamic Testing
C. Function Testing
D. Static Testing
正解:D
質問 4:
From where can clues about the underlying application environment can be collected?
A. From executable file
B. From source code
C. From the extension of the file
D. From file types and directories
正解:C
質問 5:
James is testing the ability of his routers to withstand DoS attacks. James sends ICMP ECHO requests to the broadcast address of his network. What type of DoS attack is James testing against his network?
A. Smurf
B. Trinoo
C. SYN flood
D. Fraggle
正解:A
質問 6:
What is a difference between host-based intrusion detection systems (HIDS) and network-based intrusion detection systems (NIDS)?
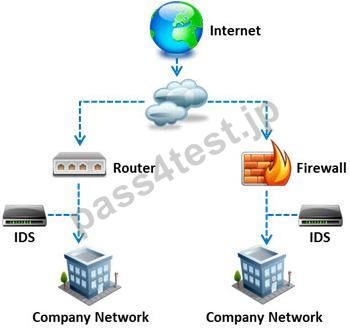
A. Attempts to install Trojans or backdoors cannot be monitored by a HIDS whereas NIDS can monitor and stop such intrusion events.
B. NIDS are usually a more expensive solution to implement compared to HIDS.
C. HIDS requires less administration and training compared to NIDS.
D. NIDS are standalone hardware appliances that include network intrusion detection capabilities whereas HIDS consist of software agents installed on individual computers within the system.
正解:D


 820 お客様のコメント
820 お客様のコメント






Yamaoka -
Pass4Testのこの問題集は参考書と過去問を解けば合格できると思います!