Identify the type of testing that is carried out without giving any information to the employees or administrative head of the organization.
A. Announced Testing
B. Blind Testing
C. Double Blind Testing
D. Unannounced Testing
正解:C
質問 2:
Identify the injection attack represented in the diagram below:
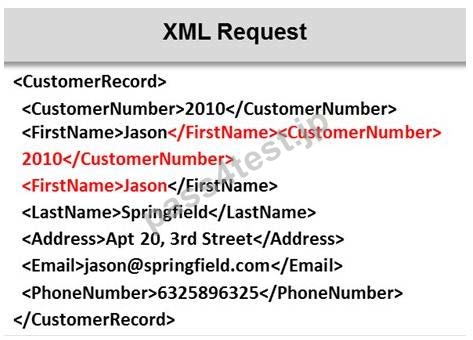
A. XPath Injection Attack
B. XML Injection Attack
C. XML Request Attack
D. Frame Injection Attack
正解:B
解説: (Pass4Test メンバーにのみ表示されます)
質問 3:
One needs to run "Scan Server Configuration" tool to allow a remote connection to Nessus from the remote Nessus clients. This tool allows the port and bound interface of the Nessus daemon to be configured. By default, the Nessus daemon listens to connections on which one of the following?
A. Localhost (127.0.0.0) and port 1243
B. Localhost (127.0.0.1) and port 1246
C. Localhost (127.0.0.1) and port 1240
D. Localhost (127.0.0.1) and port 1241
正解:D
質問 4:
Which of the following defines the details of services to be provided for the client's organization and the list of services required for performing the test in the organization?
A. Requirement list
B. Report
C. Quotation
D. Draft
正解:C
質問 5:
Which vulnerability assessment phase describes the scope of the assessment, identifies and ranks the critical assets, and creates proper information protection procedures such as effective planning, scheduling, coordination, and logistics?
A. Pre-Assessment Phase
B. Post-Assessment Phase
C. Assessment Phase
D. Threat-Assessment Phase
正解:A
質問 6:
Which of the following contents of a pen testing project plan addresses the strengths, weaknesses, opportunities, and threats involved in the project?
A. Project Goal
B. Success Factors
C. Objectives
D. Assumptions
正解:D
質問 7:
From where can clues about the underlying application environment can be collected?
A. From executable file
B. From source code
C. From the extension of the file
D. From file types and directories
E. Explanation:
QUESTIONNO: 16 Which of the following information gathering techniques collects information from an organization's web-based calendar and email services?
A. Anonymous Information Gathering
B. Private Information Gathering
C. Passive Information Gathering
D. Active Information Gathering
正解:C
解説: (Pass4Test メンバーにのみ表示されます)
質問 8:
Identify the framework that comprises of five levels to guide agency assessment of their security programs and assist in prioritizing efforts for improvement:
A. Microsoft Internet Security Framework
B. Information System Security Assessment Framework (ISSAF)
C. Nortells Unified Security Framework
D. Federal Information Technology Security Assessment Framework
正解:D


 1283 お客様のコメント
1283 お客様のコメント







Kondo -
今後ともよろしくお願い申し上げます。やはり高い的中率がありますよね。
これからも他の試験を受ける予定ですが、またよろしくね。