A user reports a pop-up error when starting a Windows machine. The error states that the machine has
been infected with a virus and instructs the user to download a new antivirus client. In which of the
following locations should the incident responder check to find what is generating the error message?
(Choose two.)
A. Event Viewer
B. Browser history
C. Programs and Features
D. Device Manager
E. Auto-start registry keys
正解:A,E
質問 2:
An analyst would like to search for a specific text string at the beginning of a line that begins with four
capital alphabetic characters. Which of the following search operators should be used?
A. /\b[A-Z]{4}\g
B. /A\w{4}\b
C. /B[A-Z]{4}\b\g
D. /\b\w{4}\b
正解:A
質問 3:
Click the exhibit button. After reviewing captured network traffic logs, a security auditor suspects a
violation of the organization's computer use policy. Which of the following is the likely indicator of the
violation?
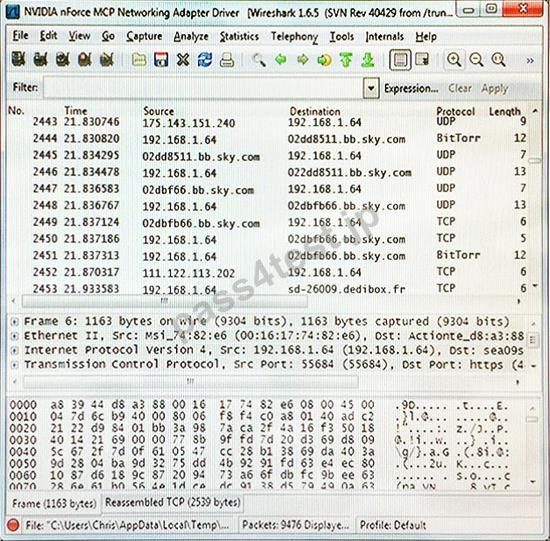
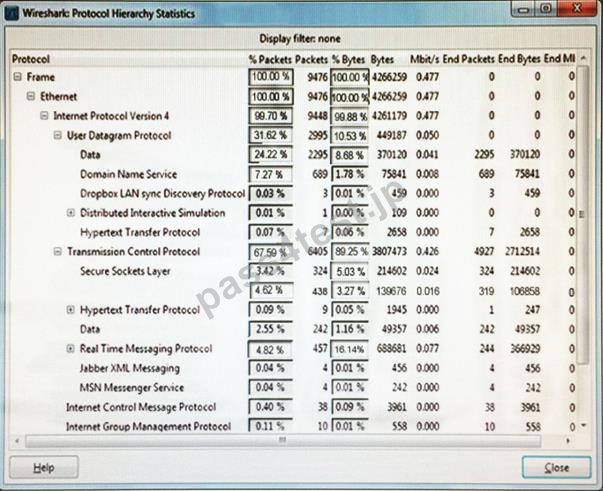
A. Unauthorized programs
B. New user account
C. Malicious software
D. Registry entries
E. Service disruption
正解:A
質問 4:
A suspicious laptop is found in a datacenter. The laptop is on and processing data, although there is no application open on the screen.
Which of the following BEST describes a Windows tool and technique that an investigator should use to analyze the laptop's RAM for working applications?
A. Net start and Network analysis
B. Volatility and Memory analysis
C. Regedit and Registry analysis
D. Task manager and Application analysis
正解:C
質問 5:
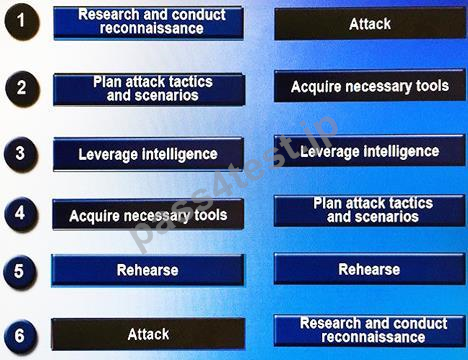
DRAG DROP
Drag and drop the following steps to perform a successful social engineering attack in the correct order,
from first (1) to last (6).
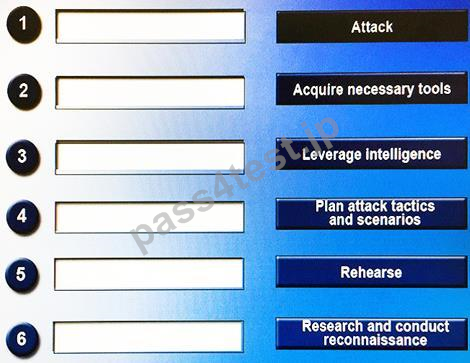
正解:


 1023 お客様のコメント
1023 お客様のコメント





Yoshida -
どうもありがとうございます!このCFR-210問題集に収めていて、本当に助けになりました。