The IP protocol was designed for use on a wide variety of transmission links. Although the maximum length of an IP datagram is 64K, most transmission links enforce a smaller maximum packet length limit, called a MTU.
The value of the MTU depends on the type of the transmission link. The design of IP accommodates MTU differences by allowing routers to fragment IP datagrams as necessary. The receiving station is responsible for reassembling the fragments back into the original full size IP datagram.
IP fragmentation involves breaking a datagram into a number of pieces that can be reassembled later. The IP source, destination, identification, total length, and fragment offset fields in the IP header, are used for IP fragmentation and reassembly.
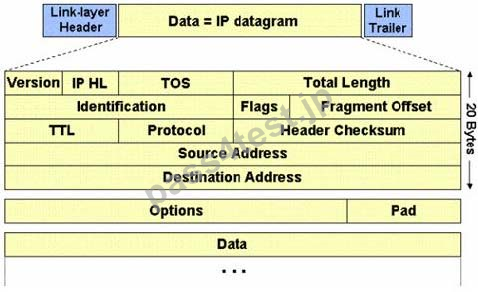
The fragment offset is 13 bits and indicates where a fragment belongs in the original IP datagram. This value is a:
A. Multiple of eight bytes
B. Multiple of two bytes
C. Multiple of six bytes
D. Multiple of four bytes
正解:A
解説: (Pass4Test メンバーにのみ表示されます)
質問 2:
One of the steps in information gathering is to run searches on a company using complex keywords in Google.

Which search keywords would you use in the Google search engine to find all the
PowerPoint presentations containing information about a target company, ROCHESTON?
A. ROCHESTON +ppt:filesearch
B. ROCHESTON filetype:ppt
C. ROCHESTON fileformat:+ppt
D. ROCHESTON ppt:filestring
正解:B
解説: (Pass4Test メンバーにのみ表示されます)
質問 3:
Traceroute is a computer network diagnostic tool for displaying the route (path) and measuring transit delays of packets across an Internet Protocol (IP) network. It sends a sequence of three Internet Control Message Protocol (ICMP) echo request packets addressed to a destination host.
The time-to-live (TTL) value, also known as hop limit, is used in determining the intermediate routers being traversed towards the destination.
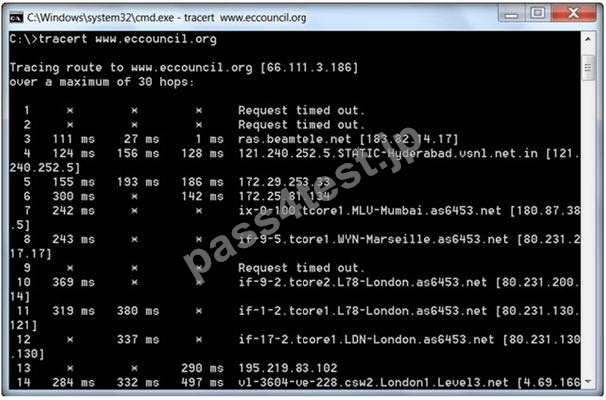
During routing, each router reduces packets' TTL value by
A. 4
B. 1
C. 3
D. 2
正解:B
解説: (Pass4Test メンバーにのみ表示されます)
質問 4:
A Blind SQL injection is a type of SQL Injection attack that asks the database true or false questions and determines the answer based on the application response. This attack is often used when the web application is configured to show generic error messages, but has not mitigated the code that is vulnerable to SQL injection.
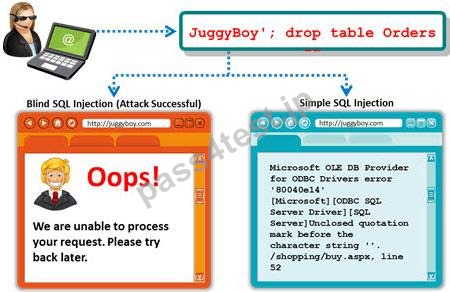
It is performed when an error message is not received from application while trying to exploit SQL vulnerabilities. The developer's specific message is displayed instead of an error message. So it is quite difficult to find SQL vulnerability in such cases.
A pen tester is trying to extract the database name by using a blind SQL injection. He tests the database using the below query and finally finds the database name.
http://juggyboy.com/page.aspx?id=1; IF (LEN(DB_NAME())=4) WAITFOR DELAY '00:00:10'--
http://juggyboy.com/page.aspx?id=1; IF (ASCII(lower(substring((DB_NAME()),1,1)))=97) WAITFOR DELAY '00:00:10'--
http://juggyboy.com/page.aspx?id=1; IF (ASCII(lower(substring((DB_NAME()),2,1)))=98) WAITFOR DELAY '00:00:10'--
http://juggyboy.com/page.aspx?id=1; IF (ASCII(lower(substring((DB_NAME()),3,1)))=99) WAITFOR DELAY '00:00:10'--
http://juggyboy.com/page.aspx?id=1; IF (ASCII(lower(substring((DB_NAME()),4,1)))=100) WAITFOR DELAY '00:00:10'--
What is the database name?
A. ABCD
B. EFGH
C. WXYZ
D. PQRS
正解:A
解説: (Pass4Test メンバーにのみ表示されます)
質問 5:
Which of the following is the objective of Gramm-Leach-Bliley Act?
A. To certify the accuracy of the reported financial statement
B. To protect the confidentiality, integrity, and availability of data
C. To set a new or enhanced standards for all U.S. public company boards, management and public accounting firms
D. To ease the transfer of financial information between institutions and banks
正解:B
解説: (Pass4Test メンバーにのみ表示されます)
質問 6:
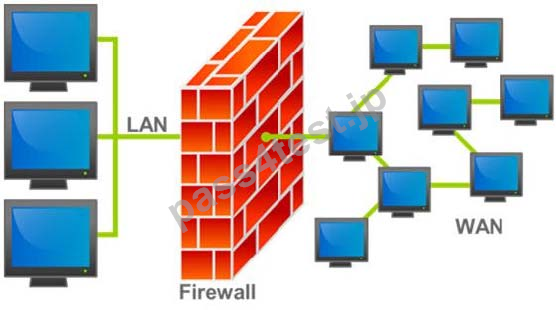
Hackers today have an ever-increasing list of weaknesses in the web application structure at their disposal, which they can exploit to accomplish a wide variety of malicious tasks.

New flaws in web application security measures are constantly being researched, both by hackers and by security professionals. Most of these flaws affect all dynamic web applications whilst others are dependent on specific application technologies. In both cases, one may observe how the evolution and refinement of web technologies also brings about new exploits which compromise sensitive databases, provide access to theoretically secure networks, and pose a threat to the daily operation of online businesses.
What is the biggest threat to Web 2.0 technologies?
A. URL Tampering Attacks
B. Service Level Configuration Attacks
C. SQL Injection Attacks
D. Inside Attacks
正解:A
質問 7:
Which of the following is NOT related to the Internal Security Assessment penetration testing strategy?
A. Testing to provide a more complete view of site security
B. Testing focused on the servers, infrastructure, and the underlying software, including the target
C. Testing including tiers and DMZs within the environment, the corporate network, or partner company connections
D. Testing performed from a number of network access points representing each logical and physical segment
正解:D


 667 お客様のコメント
667 お客様のコメント







Namiki -
解説と演習問題を掲載しているので本番でも動じない実力を養うことができます。やさしい参考書&問題集だと思います。Pass4Testはいいぞ